.env file:
.env.development
Step 1 - Create schema declaration
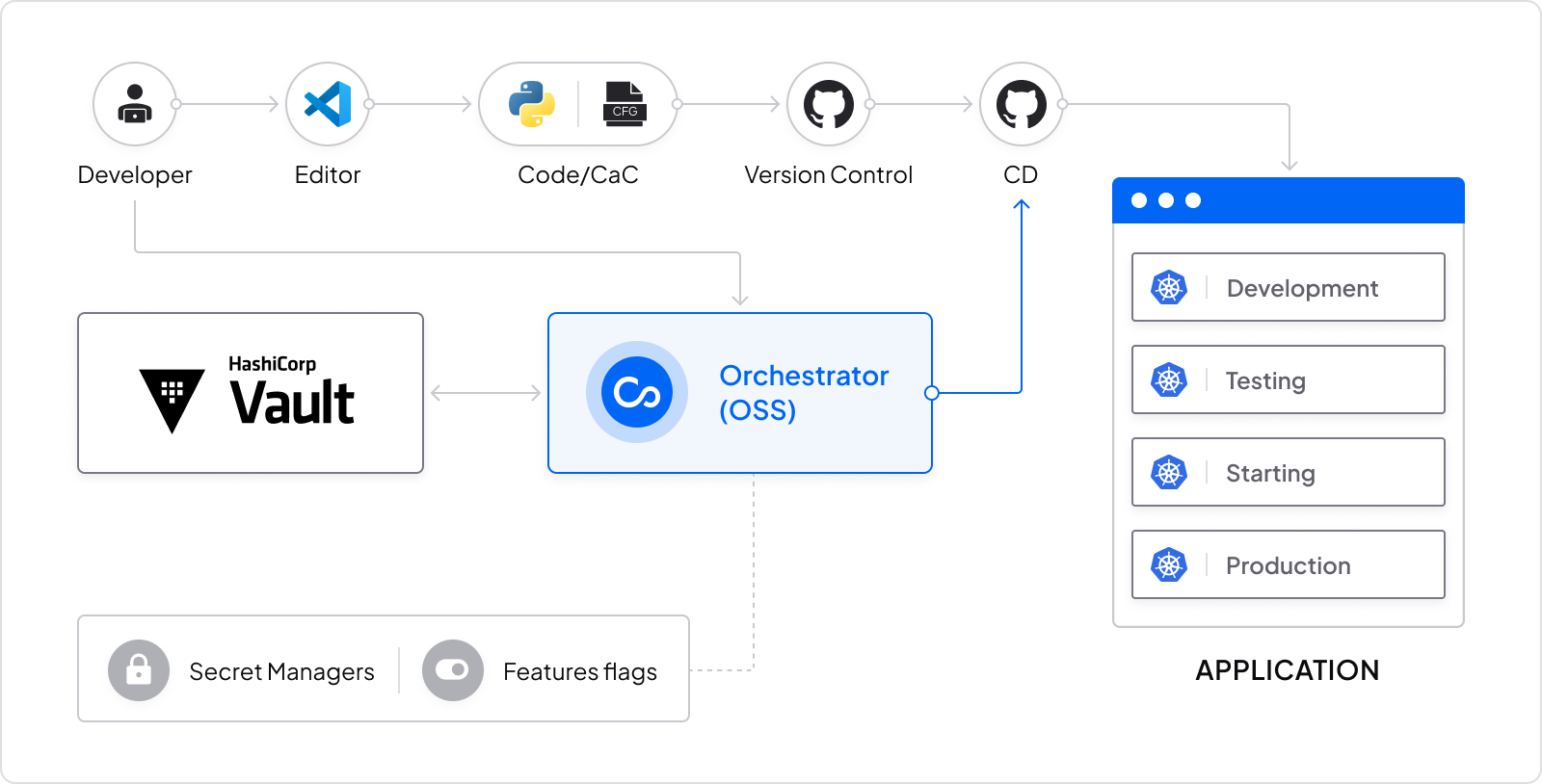
Instead of maintaining a.env file for each environment or Vault for production and possibly for other sensitive environments,
create a .cfgu schema declaration for this service, so that each change will only have to be changed once (only the key in the schema) and then the values will be initialized by the same interface.
Our schema will look like this:
my-app.cfgu.json
Step 2 - Use defaults for local development
Running a local environment was never easier, choose your preferred way to inject your environment variables:- Run Configu seamlessly with your app
- Inject the variables into your shell
- Download and use
.envfile or any other format you want

